It has been almost nine years since America was traumatized by Islamic barbarians hell-bent on destroying our freedoms. Three days after September 11th, 2001, President George W. Bush climbed upon the rubble of the fallen WTC towers and made a vow to the American people to avenge the senseless deaths orchestrated by third-world cave people. Despite his valiant efforts to command-in-chief a two-front war, sign the USA PATRIOT ACT, and push for telecom immunity for terrorist eavesdropping, Bush was weak, and did not take enough fight to the enemy.
Thank God for President Barack Obama.
[T]he Obama administration has significantly expanded a largely secret U.S. war against al-Qaeda and other radical groups, according to senior military and administration officials. Special Operations forces have grown both in number and budget, and are deployed in 75 countries, compared with about 60 at the beginning of last year. (Washington Post)
To the bleeding-hearts lefties, the weak-kneed Quaker pacifists, and the dope-smoking, anti-war, college crybabies, the phrase “secret war” has troubling implications. They decry the extra-judicial death-squad assassinations, the CIA drone attacks killing hundreds of non-combatants, rendition disappearances, and other necessary unpleasantries in the Global War of Terror (GWOT). But, they must be reminded of the fact that WE did not start this fight and sometimes you have to play dirty to win.
War is never perfect, or clean, or fair. The scraggly camel fuckers who outwitted the most technologically advanced air defense system and cunningly planned the 9-11 attack on the same day that numerous NORAD war game scenarios were scheduled punched below the belt. Osama and his boys awoke a sleeping giant that day. Unfortunately, America had to wait almost a decade before we had a ballsy and decisive leader who was willing to exact the brutal revenge that the people required.
Obama, one senior military official said, has allowed “things that the previous administration did not.”
The quote above speaks volumes. The clear implication is that by vetoing available extraterritorial and aggressive GWOT measures, Bush’s promise to “take the battle to the enemy” fell short. In contrast, President Obama is a man who refuses to allow international law (which is thoroughly anti-American) or the pesky opinions of the international community to dictate the manner in which justice must be served. One condemnation coming from a United Nations report “questioned the administration’s authority under international law to conduct such raids, particularly when they kill innocent civilians.” Must the feckless U.N. diplomats be reminded that it was the U.S. financial center and the Pentagon that was attacked on 9-11, and not their shitty Turtle Bay monolith full of stuffed shirts and foreign accents.
Now, America has a brave and dedicated leader who not only grasps the existential threat posed by the Moslem cave people, but is willing to cut them off at the knees. President Obama has not forgotten the scores of Koran-thumping sleeper cells in this country patiently awaiting their bomb mission orders. He is also cognizant of the ever-present urban center dirty nuke threat that could make 9-11 look like a rookie outing. Soon, America will know true peace, once Islamic terrorism (and all other anti-American sentiment) is dealt the knockout punch.
I’ve got two daughters, nine and six years old. I am going to teach them first of all about values and morals. But if they make a mistake, I do not want them punished with a baby ~ President Barack H. Obama (America’s 44th President)


 Thus, those who employ secret police agencies must monitor them, to be sure they are not acquiring too much power.
Thus, those who employ secret police agencies must monitor them, to be sure they are not acquiring too much power.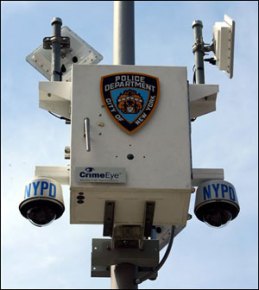 In spying-and-hiding transactions, worry leads to more worry and suspicion leads to more suspicion. The very act of participating, however unwillingly, in the secret police game – even as victim, or citizen being monitored – will eventually produce all the classic symptoms of clinical paranoia.
In spying-and-hiding transactions, worry leads to more worry and suspicion leads to more suspicion. The very act of participating, however unwillingly, in the secret police game – even as victim, or citizen being monitored – will eventually produce all the classic symptoms of clinical paranoia.








Recent Comments